Lab 7 – Single-Sign-On Across Authentication Domains¶
In this lab, we will show you how to provide SSO across multiple applications. Normally APM will require authentication each time an application is accessed. By using a Domain Cookie it is possible to re-use an existing APM session to access multiple applications.
Note
Lab Requirements:
- Previous Labs 5 and 6 successfully completed
Task – Verify Authentication Required for different applications¶
- Open a Private web browser or clear your browser cache and go to the Virtual Server used earlier https://basic.f5demo.com
- You should be able to logon with the following credentials:
- Username: user
- Password: Agility1
- Once successfully logged in, you will be presented with the same information page you observed earlier from basic.f5demo.com “App #1”.
- Now go to https://app2.f5demo.com you should be prompted to logon again.
- You should be able to logon with the following credentials:
- Username: user
- Password: Agility1
- Once successfully logged in, you will be presented with information about “App #2”.
- Logout and close the browser window.
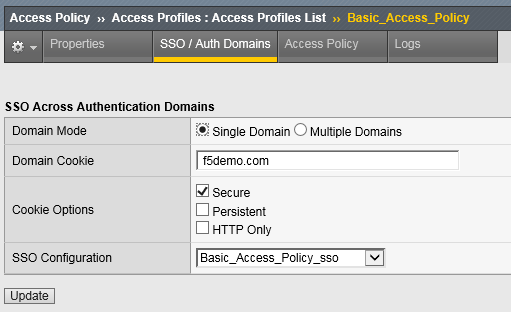
Task - Specify Domain Cookie¶
Task - Testing Authentication across domains¶
- Open a Private web browser or clear your browser cache and go to the Virtual Server used earlier https://basic.f5demo.com
- You should be able to logon with - Username: user - Password: Agility1
- Once successfully logged in, you will be presented with the same information page you observed earlier.
- Now go to https://app2.f5demo.com. You should not be prompted to logon again!
Task 4 (Bonus) - Authentication across domains & virtual servers¶
Repeat the previous steps, but for Forms_Access_Policy instead of Basic_Access_Policy.
Are you prompted for authentication when going from https://forms.f5demo.com to https://basic.f5demo.com?
Try changing the value for “Profile Scope” for Basic_Access_Policy and Forms_Access_Policy from Profile to Global
*Troubleshooting tips:
Did you forget to Apply Access Policy ?
Verify the Domain Cookie configured on the SSO page… for both policies?